Oct
25
TTT Part 23 of n – Networking Intro
Filed Under Computers & Tech, System Administration on October 25, 2014 | 11 Comments
This instalment is the first in what will probably be quite a long mini-series on computer networking. Before we can look at the terminal commands that allow us to interact with the network, we need to gain an understanding of how computer networking works. This is a complex topic, ad there’s a lot to take in. The individual pieces don’t make sense without keeping the big-picture in mind, and yet the big picture doesn’t gel together until you start to understand the detail. Bearing that in mind, this instalment starts the series with a big-picture overview. We’ll flesh this overview out over the instalments that follow, adding in the detail that will hopefully make the whole thing click for you. Ultimately, it’s actually a very elegant design, but that elegance may not be immediately obvious!
Oct
24
“Behind People’s Backs”
Filed Under Security, Computers & Tech on October 24, 2014 | 2 Comments
I’m fed up with people being dishonest about the new search feature in Yosemite. You can have reasonable discussions about the pros and cons of this feature, but for goodness sake enough with the fact-free hyperbole.
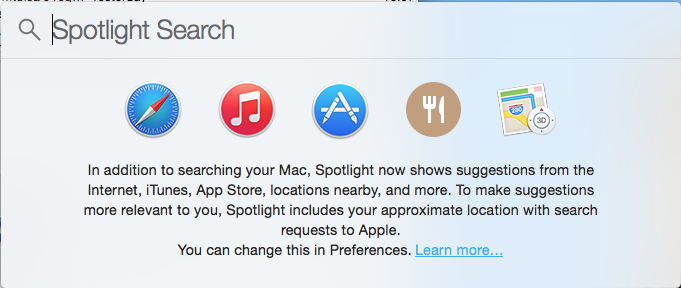
I’ve lost count of how many people insist Apple is sending this information back to Apple “behind people’s backs”. Sorry, but that is a fact-free assertion. The screenshot below shows the search feature in question:
Here it is again with the important aspects highlighted:
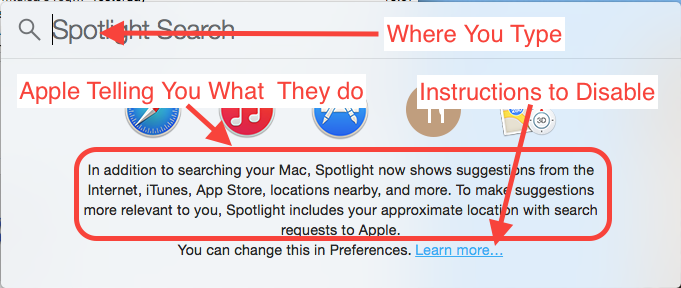
If that’s “behind people’s backs” then I’m the pope!
Something I will agree with critics on is that I think that link to instructions should be a button or checkbox to disable the feature. A link to instructions is nice, a button would be perfect!
This data is not being sent for no reason, it’s being sent to offer people a richer search experience, and Apple were actually playing catchup in this regard. Here’s what Microsoft say Windows 8.1 does:
By default, the Search charm searches the apps, files, and settings on your PC and OneDrive, plus the web.
The real question is whether or not Apple have thought about our privacy when implementing this feature, and whether or not they have designed the feature well. Here is what Apple say they do:
We are absolutely committed to protecting our users’ privacy and have built privacy right into our products. For Spotlight Suggestions we minimize the amount of information sent to Apple. Apple doesn’t retain IP addresses from users’ devices. Spotlight blurs the location on the device so it never sends an exact location to Apple. Spotlight doesn’t use a persistent identifier, so a user’s search history can’t be created by Apple or anyone else. Apple devices only use a temporary anonymous session ID for a 15-minute period before the ID is discarded.
We also worked closely with Microsoft to protect our users’ privacy. Apple forwards only commonly searched terms and only city-level location information to Bing. Microsoft does not store search queries or receive users’ IP addresses.
You can also easily opt out of Spotlight Suggestions, Bing or Location Services for Spotlight.
So, your searches are not tied to your Apple ID or any other persistent ID, instead, your device creates a new random identifier every 15 minutes, so your searches are anonymous, and most importantly, they can’t be profiled because the IDs are ephemeral. The fact that the device fuzzes the location before sending it on is also very good. The fact that IP details are not logged is also good. Finally, the fact that only a sub-set of the request is sent on to Bing is great.
I do not believe Apple would blatantly lie to users. For a start, as a publicly traded company that would almost certainly be criminal, but even leaving that aside, it would be spectacularly damaging for Apple to be caught lying about stuff like this.
Bottom line, Apple have been very open about this, Apple have implemented this feature with privacy in mind, and this feature is not unique to Apple OSes. Finally, if you want to opt-out, you can.
If this really is such a scandal, why is Windows 8.1 not coming under the same fire? *cough* link bait *cough*
Oct
10
TTT Part 22 of n – Tips & Tricks
Filed Under Computers & Tech, System Administration on October 10, 2014 | 2 Comments
This instalment is a little breather between the fairly heavy instalments on searching, and the upcoming set of instalments on networking. We’ll start with a look at some tips and tricks for getting the most out of BASH, and then transition to some tips and tricks for getting the most out of the OS X Terminal app.
Sep
30
OS X Service for Markdown Link Creation
Filed Under Software Development, Computers & Tech on September 30, 2014 | Leave a Comment
At the request of listeners I’m going to be publishing a big list of links with future Let’s Talk Apple shows. The logical format for me to create those notes in is Markdown – it’s plain text, and quick and easy for me to add new items and re-arrange them into logical groupings. for the most part markdown has little to no overhead, but when it comes to links there is a little work. What I wanted was a way of automatically taking a URL, and turning it into a markdown link where the text for the link is the site the story is from with /… after it.
When all is done I want to turn a url like http://www.macobserver.com/tmo/article/every-important-link-from-apples-9-9-event-on-one-page into a link that looks like: www.macobserver.com/…. In other words, I need to take the URL above as input, and turn it into the following Markdown code:
[www.macobserver.com/...](http://www.macobserver.com/tmo/article/every-important-link-from-apples-9-9-event-on-one-page)
My reason for choosing this format is that I want to give obvious credit to the sources of the stories, but not waste screen real-estate on long URLs.
Perl’s URI module can interpret URLs, and easily extract the host part of the URL, OS X Services can take selected text as input and replace it with processed output, Automator can create OS X Services, and Automator can execute Perl code. By putting all these pieces together I was able to solve my problem in just 20 minutes with a few clicks and a few lines of code.
You can just download the service with the link below, or you can read on to see how it’s done.
Download OS X Service …
Sep
26
TTT Part 21 of n – More Searching
Filed Under System Administration, Computers & Tech on September 26, 2014 | 1 Comment
This is the third and final instalment on searching. In the first instalment we learned how to search for text within files and streams using egrep. In the second we learned to search for files based on all sorts of criteria with the find command. In this final instalment we’ll start by looking at one last feature of find, its a ability to execute commands on the files it finds. Then we’ll end by looking at an OS X-only alternative to find that makes use of the Spotlight search index to really speed up searches.
Sep
7
TTT Part 20 of n – File Searches
Filed Under System Administration, Computers & Tech on September 7, 2014 | 2 Comments
In the previous previous instalment we looked at using egrep to search for a particular piece of text in a stream or file. egrep is often a great tool for finding a file you are looking for, but only if the file is a plain text file, and only if you are searching for that file based on its content. What if you want to search for files based on other criteria, like the last time the file was edited, or the name of the file, or the size of the file, or the type of the file etc.? For that you need a different command, for that you need find.
Aug
30
Play a Sound in Automator
Filed Under System Administration, Software Development, Computers & Tech on August 30, 2014 | 5 Comments
In a recent Chit Chat Across the Pond segment on episode 484 of the Nosillacast Mac Podcast myself and Allison walked through the process of creating an automator action for generating secure memorable passwords with the XKPasswd 2 perl module (we basically walked through the steps in this blog post). During that discussion Allison mentioned it would nice if Automator could play a sound when it was finished so you could know when automator was done generating the password without installing a third-party notification app like Growl.
At the time I didn’t know of a way to do that, but now I do, and it’s really quite straightforward thanks to the OS X terminal command afplay which will play an audio file without opening any sort of GUI.
Aug
16
Creating an XKPasswd 2 OS X Service with Automator
Filed Under System Administration, Computers & Tech on August 16, 2014 | 5 Comments
It’s going to take me a few months to re-write the www.xkpasswd.net site so it uses the new XKPasswd 2 perl module. In the mean-time, thanks to the magic of Automator an OSX Services, Mac users can integrate XKPasswd 2 right into their OS with out very much effort at all.
This blog post is intended as a follow-on post to my earlier XKPasswd 2 beginners guide. This post assumes you have followed the installation instructions in the beginner’s guide to install the XKPasswd 2 module, that you followed along with that post and created a script that generates passwords in a format of your choice, and that you have tested that script to be sure it works. In this post I’ll be using the final example script from the beginner’s guide as my pre-written script.
Aug
16
XKPasswd 2 – An Absolute Beginner’s Guide
Filed Under Software Development, Computers & Tech on | 3 Comments
I’ve just released version two of the XKPasswd perl module, the module that powers the www.xkpasswd.net website. At the moment, only the module has been updated, not the website. It’s going to take me a few months to make all the changes I want to on that site. In the mean time you, can use the module directly. The prerequisites are that you have a computer with Perl and GIT installed, and a plain text editor (no difficult on Linux or Mac).
Aug
13
Announcing XKPasswd.pm 2
Filed Under My Projects, Security, Software Development, Computers & Tech on August 13, 2014 | Leave a Comment
It’s hard to believe, but it’s been nearly three years since I released my first attempt at a Perl library for generating secure memorable passwords. The original spark of inspiration came when Steve Gibson released and talked about his Password Haystacks page at around the same time as the now famous correct horse battery staple XKCD comic was released. Take the idea of using words as the basis for passwords from XKCD, add computers to introduce real randomness (we humans are terrible at being random), and season with come well-chosen and intuitively placed symbols and digits to increase the size of your haystack, and voila, passwords are are both human-friendly and secure!
The first version of the library worked, as evidenced by it’s years of service powering www.xkpasswd.net. That’s not a bad start. But, it was a first attempt at solving the problem, and, I was still a Perl padawan back then. Some of my early design decisions resulted in a less than ideal API making the library a lot less developer-friendly than it could have been, and I’ve learned a lot about Perl, and Perl best practices since 2011!
I’ve spent the past half year or so re-implementing the same basic idea from scratch. In terms of functionality very little has changed, there are a few additions, but the big change is in the API. Basically, the old API was a mess – you needed one config hashref to instantiate the object, then a different config hashref to call the password generation function. Nonsense! That’s not intuitive, not obvious, and not efficient! The new API allows you to achieve the same result with less code, and the code you will have will be easier to read and understand.
You’ll find the project page for the new library at the link below – this page provides links for downloading the code, and links to the module’s very detailed documentation.
This module is provided entirely for free, but has taken a considerable amount of time and effort to write, and continues to take time to develop and maintain. Please consider making a small contribution towards the time I dedicate to this project.
XKPasswd 2 Project Page (http://bartb.ie/xkpasswd)






